How to Manage Next-Gen SD-WAN Using Policies and Application-Awareness
As with most things, the more advanced the SD-WAN is, the more effective it will be in meeting business objectives, providing deployment flexibility, and ensuring IT operations are future-proofed.
Network Policy
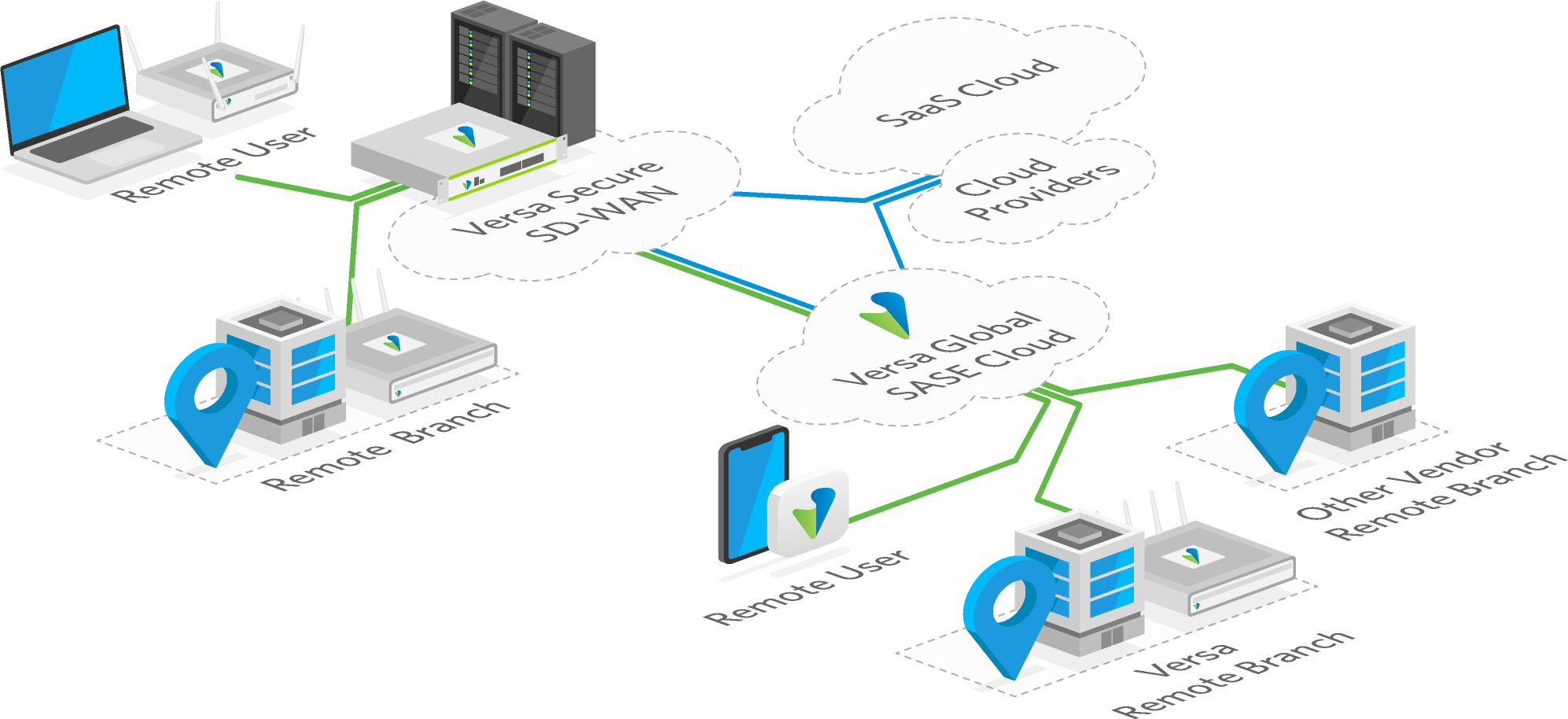
A next-gen SD-WAN will understand individual application SLA requirements and translate them into policies to which the network must adhere. This provides proactive network and application monitoring to ensure optimal traffic delivery and a quality user experience, whether on-premises, private/public cloud, or SaaS.
Application Awareness
An automated policy-based framework is propagated through unified control and management, from an easy-to-use, single-pane-of-glass interface. Visibility is enhanced, providing IT with insights into applications, devices, users, and networking, to ensure all functions adhere to the organization’s business intent. This simplifies IT’s ability to define, control, and change business requirements across their branches, data centers, and cloud/SaaS.
Centralized management using simple, template-driven workflows eliminates monotonous, error-prone configuration. Cloud-based SD-WAN workflows make it easy to propagate new branches with zero-touch, with consistent and error-free SD-WAN deployment.